Price:
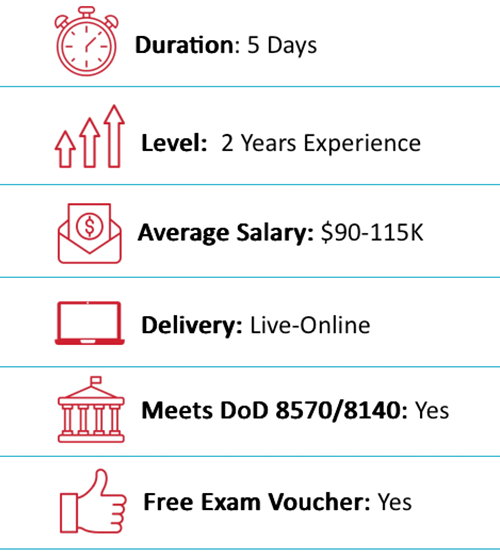
$3,495
Duration:
5 Days or 10 Nights
Delivery Method:
Online Live/On-Demand Live
Overview
Outline
Training Includes
Audience
About Exam
About the Instructor
Eric Reed Exclusives

Certified Network Defender (CND) Overview
Certified Network Defender (CND) is a vendor-neutral, hands-on, instructor-led comprehensive network security certification training program. It is a skills-based, lab intensive program based on a job-task analysis and Cybersecurity education framework presented by the National Initiative of Cybersecurity Education (NICE). The course has also been mapped to global job roles and responsibilities and the Department of Defense (DoD) job roles for system/network administrators. The course is designed and developed after extensive market research and surveys. The program prepares network administrators on network security technologies and operations to attain Defense-in-Depth network security preparedness. It covers the protect, detect and respond approach to network security. The course contains hands-on labs, based on major network security tools and techniques which will provide network administrators real world expertise on current network security technologies and operations. The study-kit provides you with over 10 GB of network security best practices, assessments and protection tools. The kit also contains templates for various network policies and a large number of white papers for additional learning.

Certified Network Defender (CND) Outline
Module 1: Network Attacks and Defense Strategies
- Essential network security attack terminology
- Network-level attack techniques
- Host-level attack techniques
- Application-level attack techniques
- Social engineering attack techniques
- Email attack techniques
- Mobile device attack techniques
- Cloud attack techniques
- Wireless network attack techniques
- Hacking methodologies and frameworks
- Fundamentals of network defense
- Continual/adaptive security strategy
- Defense-in-depth security strategy
Module 2: Administrative Network Security
- Compliance with regulatory frameworks, laws, and acts
- Designing and developing security policies
- Conducting security awareness training
- Administrative security measures
- Asset management and staying current on security trends
Module 3: Technical Network Security
- Access control principles, terminologies, and models
- Identity and Access Management concepts
- Cryptographic security techniques and algorithms
- Network segmentation security benefits
- Essential network security solutions and protocols
Module 4: Network Perimeter Security
- Firewall security concepts, topologies, and deployment
- Hardware, software, host, internal, and network firewall types
- Deep packet inspection and secure firewall implementation
- Router and switch security measures
- IDS/IPS deployment, false positives/negatives, and IDS classifications
- Zero Trust Model and Software-Defined Perimeter (SDP) concepts
Module 5: Endpoint Security — Windows Systems
- Windows OS security concerns and components
- User account and password management
- Patch management and security hardening
- Active Directory security best practices
- Windows network services and protocol security
Module 6: Endpoint Security — Linux Systems
- Linux OS security fundamentals
- Linux hardening and patching
- User access and password management
- Linux network security and remote access
- Linux security tools and frameworks
Module 7: Endpoint Security — Mobile Devices
- Enterprise mobile usage policies and risk mitigation
- Mobile security management solutions
- Security guidelines for Android devices
- Security guidelines for iOS devices
Module 8: Endpoint Security — IoT Devices
- IoT ecosystem and communication models
- IoT security challenges and risks
- Securing IoT environments and best practices
- IoT security standards and initiatives
Module 9: Administrative Application Security
- Application whitelisting and blacklisting
- Application sandboxing
- Application patch management
- Web Application Firewall (WAF) implementation
Module 10: Data Security
- Data security principles and importance
- Data encryption (at rest and in transit)
- Data masking concepts
- Data backup and retention strategies
- Secure data destruction and DLP (data loss prevention)
Module 11: Enterprise Virtual Network Security
- Virtualization security fundamentals
- Network Virtualization (NV), SDN, NFV security
- OS virtualization security
- Container, Docker, and Kubernetes security best practices
Module 12: Enterprise Cloud Security
- Cloud computing fundamentals
- Cloud security principles
- Security in AWS, Azure, and GCP environments
- Cloud security tools and best practices
Module 13: Wireless Network Security
- Wireless network fundamentals
- Wireless encryption and authentication mechanisms
- Wireless network security implementation measures
Module 14: Network Traffic Monitoring and Analysis
- Network monitoring concepts and setup
- Baseline traffic signatures
- Traffic analysis with tools such as Wireshark
- Network anomaly detection and bandwidth monitoring
Module 15: Network Logs Monitoring and Analysis
- Logging fundamentals
- Windows, Linux, and macOS log analysis
- Firewall, router, and web server log analysis
- Centralized log monitoring and analysis
Module 16: Incident Response and Forensics Investigation
- Incident response concepts
- First responder roles and processes
- Forensic investigation fundamentals
- Evidence collection and examination
Module 17: Business Continuity and Disaster Recovery
- Business continuity planning concepts
- Disaster recovery strategies
- BCP and DRP development and standards
Module 18: Risk and Vulnerability Management
- Risk management concepts and frameworks
- Vulnerability scanning and assessment programs
- Attack surface reduction techniques
Module 19: Threat Assessment with Attack Surface Analysis
- Attack surface concepts
- Indicators of exposure (IoE) identification
- Attack simulation and surface reduction
Module 20: Threat Prediction with Cyber Threat Intelligence
- Role of threat intelligence in network defense
- Types of threat intelligence
- Indicators of compromise (IoC) and indicators of attack (IoA)
- Leveraging threat intelligence for proactive defense

Certified Network Defender (CND) Training Includes
- 25-Year Veteran Instructor with Over 60,000 Students Trained and the Best Pass Rates in the Industry
- 10-Time EC-Council Instructor of the Year / 7-Time Instructor Circle of Excellence
- “Pass on the First Attempt!” Guarantee
- Online Live Instructor Led Training
- 1 Year Access to Training Session Recordings
- Official EC-Council Courseware
- Official Virtual Lab Environment
- Fast-Track Exam Preparation
- Written Exam Voucher
- Practical Exam Voucher
- After Class Support and Mentoring

Certified Network Defender (CND) Audience
- Network Administrators
- Network security Administrators
- Network Security Engineer
- Network Defense Technicians
- CND Analyst
- Security Analyst
- Security Operator
- Anyone involved in network operations

About Certified Network Defender (CND) Exam
The Certification exam is included with the camp and is administered on the final day.
- Exam title: CND
- Exam code: 312-38
- Number of questions: 100
- Duration: 4 Hours
- Availability: ECC Exam
- Test Format: Interactive Multiple Choice Questions

About the Certified Network Defender (CND) Instructor
Eric Reed is a nationally recognized cybersecurity instructor and founder of Eric Reed Cybersecurity Training, with over 25 years of experience developing mission-ready IT and security professionals. A Master Certified EC-Council Instructor and 10-time Instructor of the Year—including the 2024 CEH Instructor of the Year from EC-Council—Eric has trained more than 60,000 students worldwide across certifications including CompTIA Security+, CySA+, PenTest+, CISSP, and CEH.
Renowned for his engaging teaching style and unmatched pass rates, Eric has delivered training for leading organizations across defense, government, healthcare, finance, and technology—including Boeing, Lockheed Martin, Verizon, the U.S. Department of Defense, and the Mayo Clinic. His programs emphasize real-world application, DoD 8140/NICE alignment, and first-attempt success, helping individuals and teams strengthen their defenses and advance their careers in cybersecurity.
DoD 8570/8140-Approved:
Career Roles You Can Access with Certified Network Defender (CND)
 IAT Level I–II
IAT Level I–II
 IAM Level I
IAM Level I
CSSP Infrastructure Support
 Network Operations Specialist (441)
Network Operations Specialist (441)
 System Administrator (451)
System Administrator (451)
 Cyber Defense Infrastructure Support (521)
Cyber Defense Infrastructure Support (521)
 Cyber Defense Analyst (511)
Cyber Defense Analyst (511)
 Cyber Operator (521)
Cyber Operator (521)
What Job Titles are Most Common for People with Certified Network Defender (CND) Certification?
Some common positions that this certification can help you land include:
What our Students say
The Best EC-Council CND Training With Eric Reed Cybersecurity Training
“Pass on the First Attempt!” – Our top priority is to equip our students with both the certification and practical knowledge necessary to excel in their field. Through our optimized delivery format, which includes live instruction, hands-on labs, and rigorous exam preparation, we are able to produce unparalleled success rates. Our methodology has been proven to prepare students for real-world scenarios, ensuring that they are able to apply their skills with confidence.
Take your career to the next level with our instructor led, live online and onsite training!
EC-Council CND Training. Exam Preparation and Training
Our training programs utilize concise, specially designed slides to facilitate a deeper understanding of complex security concepts. These slides are created by our expert developers and are aimed at providing an optimal learning experience. The course, led by Eric Reed – a Master Certified CompTIA Instructor and 9-time recipient of EC- Council’s Instructor of the Year award, spans a 5-day (or 10-evening) period and is designed to be highly interactive, featuring practical exercises to ensure that students acquire the necessary skills to succeed in the industry.