Price:
$3,495
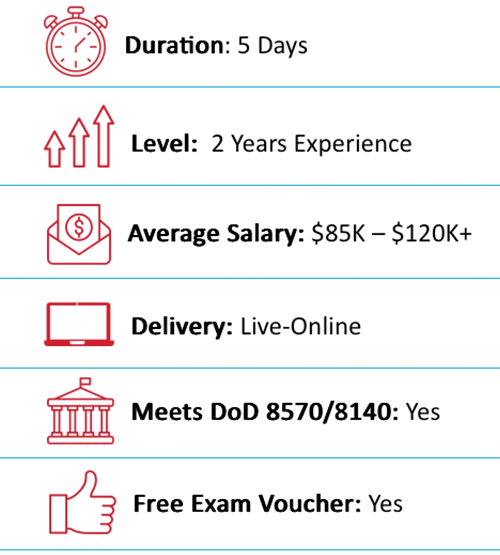
Duration:
5 Days or 10 Nights
Delivery Method:
Online Live/On-Demand Live
Overview
Outline
Training Includes
Audience
About Exam
About the Instructor
Eric Reed Exclusives

EC-Council C|HFI Overview
Digital forensic practices stem from forensic science, the science of collecting and examining evidence or materials. Digital or computer forensics focuses on the digital domain including computer forensics, network forensics, and mobile forensics. As the cyber security profession evolves, organizations are learning the importance of employing digital forensic practices into their everyday activities. Computer forensic practices can help investigate attacks, system anomalies, or even help system administrators detect a problem by defining what is normal functional specifications and validating system information for irregular behaviors.
In the event of a cyber-attack or incident, it is critical investigations be carried out in a manner that is forensically sound to preserve evidence in the event of a breach of the law. Far too many cyber-attacks are occurring across the globe where laws are clearly broken and due to improper or non-existent forensic investigations, the cyber criminals go either unidentified, undetected, or are simply not prosecuted.
Cybersecurity professionals who acquire a firm grasp on the principles of digital forensics can become invaluable members of Incident Handling and Incident Response teams. The Computer Hacking Forensic Investigator course provides a strong baseline knowledge of key concepts and practices in the digital forensic domains relevant to today’s organizations. CHFI provides its attendees a firm grasp on the domains of digital forensics.

EC-Council C|HFI Outline
Module 1: Computer Forensics in Today’s World
- Understand the Fundamentals of Computer Forensics
- Understand Cybercrimes and Their Investigation Procedures
- Understand Digital Evidence
- Understand Forensic Readiness, Incident Response, and the Role of SOC (Security Operations Center) in Computer Forensics
- Identify the Roles and Responsibilities of a Forensic Investigator
- Understand the Challenges Faced in Investigating Cybercrimes
- Understand Legal Compliance in Computer Forensics
Module 2: Computer Forensics Investigation Process
- Understand the Forensic Investigation Process and Its Importance
- Understand the Pre-investigation Phase
- Understand First Response
- Understand the Investigation Phase
- Understand the Post-investigation Phase
Module 3: Understanding Hard Disks and File Systems
- Describe Different Types of Disk Drives and Their Characteristics
- Explain the Logical Structure of a Disk
- Understand Booting Process of Windows, Linux, and Mac Operating Systems
- Understand Various File Systems of Windows, Linux, and Mac Operating Systems
- Examine File System Using Autopsy and The Sleuth Kit Tools
- Understand Storage Systems
- Understand Encoding Standards and Hex Editors
- Analyze Popular File Formats Using Hex Editor
Module 4: Data Acquisition and Duplication
- Understand Data Acquisition Fundamentals
- Understand Data Acquisition Methodology
- Prepare an Image File for Examination
Module 5: Defeating Anti-forensics Techniques
- Understand Anti-forensics Techniques
- Discuss Data Deletion and Recycle Bin Forensics
- Illustrate File Carving Techniques and Ways to Recover Evidence from Deleted Partitions
- Explore Password Cracking and Bypassing Techniques
- Detect Steganography, Hidden Data in File System Structures, Trail Obfuscation, and File Extension Mismatch
- Understand Techniques of Artifact Wiping, Overwritten Data and Metadata Detection, and Encryption
- Detect Program Packers and Footprint Minimizing Techniques
- Understand Anti-forensics Countermeasures
Module 6: Windows Forensics
- Collect Volatile and Non-volatile Information
- Perform Windows Memory and Registry Analysis
- Examine the Cache, Cookie, and History Recorded in Web Browsers
- Examine Windows Files and Metadata
- Understand ShellBags, LNK Files, and Jump Lists
- Understand Text-based Logs and Windows Event Logs
Module 7: Linux and Mac Forensics
- Understand Volatile and Non-volatile Data in Linux
- Analyze Filesystem Images Using The Sleuth Kit
- Demonstrate Memory Forensics Using Volatility and PhotoRec
- Understand Mac Forensics
Module 8: Network Forensics
- Understand Network Forensics
- Explain Logging Fundamentals and Network Forensic Readiness
- Summarize Event Correlation Concepts
- Identify Indicators of Compromise (IoCs) from Network Logs
- Investigate Network Traffic
- Perform Incident Detection and Examination with SIEM Tools
- Monitor and Detect Wireless Network Attacks
Module 9: Malware Forensics
- Define Malware and Identify the Common Techniques Attackers Use to Spread Malware
- Understand Malware Forensics Fundamentals and Recognize Types of Malware Analysis
- Understand and Perform Static Analysis of Malware
- Analyze Suspicious Word and PDF Documents
- Understand Dynamic Malware Analysis Fundamentals and Approaches
- Analyze Malware Behavior on System Properties in Real-time
- Analyze Malware Behavior on Network in Real-time
- Describe Fileless Malware Attacks and How They Happen
- Perform Fileless Malware Analysis Emotet
Module 10: Investigating Web Attacks
- Understand Web Application Forensics
- Understand Internet Information Services (IIS) Logs
- Understand Apache Web Server Logs
- Understand the Functionality of Intrusion Detection System (IDS)
- Understand the Functionality of Web Application Firewall (WAF)
- Investigate Web Attacks on Windows-based Servers
- Detect and Investigate Various Attacks on Web Applications
Module 11: Dark Web Forensics
- Understand the Dark Web
- Determine How to Identify the Traces of Tor Browser During Investigation
- Perform Tor Browser Forensics
Module 12: Cloud Forensics
- Understand the Basic Cloud Computing Concepts
- Understand Cloud Forensics
- Understand the Fundamentals of Amazon Web Services (AWS)
- Determine How to Investigate Security Incidents in AWS
- Understand the Fundamentals of Microsoft Azure
- Determine How to Investigate Security Incidents in Azure
- Understand Forensic Methodologies for Containers and Microservices
Module 13: Investigating Email Crimes
- Understand Email Basics
- Understand Email Crime Investigation and Its Steps
- U.S. Laws Against Email Crime
Module 14: Mobile Forensics
- Understand the Importance of Mobile Device Forensics
- Illustrate Architectural Layers and Boot Processes of Android and iOS Devices
- Explain the Steps Involved in Mobile Forensics Process
- Investigate Cellular Network Data
- Understand SIM File System and Its Data Acquisition Method
- Illustrate Phone Locks and Discuss Rooting of Android and Jailbreaking of iOS Devices
- Perform Logical Acquisition on Android and iOS Devices
- Perform Physical Acquisition on Android and iOS Devices
- Discuss Mobile Forensics Challenges and Prepare Investigation Report
Module 15: IoT Forensics
- Understand IoT and IoT Security Problems
- Recognize Different Types of IoT Threats
- Understand IoT Forensics
- Perform Forensics on IoT Devices

EC-Council C|HFI Training Includes
- 25-Year Veteran Instructor with Over 60,000 Students Trained and the Best Pass Rates in the Industry
- 10-Time EC-Council Instructor of the Year / 7-Time Instructor Circle of Excellence
- “Pass on the First Attempt!” Guarantee
- Online Live Instructor Led Training
- 1 Year Access to Training Session Recordings
- Official EC-Council Courseware
- Official Virtual Lab Environment
- Fast-Track Exam Preparation
- Written Exam Voucher
- After Class Support and Mentoring

EC-Council C|HFI Audience
- Police and other law enforcement personnel
- Defense and Military personnel
- e-Business Security professionals
- Systems administrators
- Legal professionals
- Banking, Insurance and other professionals
- Government agencies
- IT managers

About EC-Council C|HFI Exam
- Exam title: CHFI
- Exam code: 312-49
- Number of questions: 150
- Duration: 4 Hours
- Availability: ECC Exam Portal
- Test Format: Multiple Choice Questions

About the EC-Council C|HFI Instructor
Eric Reed is a nationally recognized cybersecurity instructor and founder of Eric Reed Cybersecurity Training, with over 25 years of experience developing mission-ready IT and security professionals. A Master Certified EC-Council Instructor and 10-time Instructor of the Year—including the 2024 CEH Instructor of the Year from EC-Council—Eric has trained more than 60,000 students worldwide across certifications including CompTIA Security+, CySA+, PenTest+, CISSP, and CEH.
Renowned for his engaging teaching style and unmatched pass rates, Eric has delivered training for leading organizations across defense, government, healthcare, finance, and technology—including Boeing, Lockheed Martin, Verizon, the U.S. Department of Defense, and the Mayo Clinic. His programs emphasize real-world application, DoD 8140/NICE alignment, and first-attempt success, helping individuals and teams strengthen their defenses and advance their careers in cybersecurity.
DoD 8570/8140-Approved:
Career Roles You Can Access with EC-Council C|HFI
 CSSP Infrastructure Support
CSSP Infrastructure Support
 CSSP Incident Responder
CSSP Incident Responder
 Forensics Analyst (531)
Forensics Analyst (531)
 Cyber Defense Incident Responder (531)
Cyber Defense Incident Responder (531)
 Vulnerability Assessment Analyst (541)
Vulnerability Assessment Analyst (541)
 Cyber Defense Auditor (671)
Cyber Defense Auditor (671)
 Threat/Warning Analyst (671)
Threat/Warning Analyst (671)
What Job Titles are Most Common for People with EC-Council C|HFI Certification?
Some common positions that this certification can help you land include:
What our Students say
The Best EC-Council Computer Hacking Forensic Investigator Training With Eric Reed Cybersecurity Training
“Pass on the First Attempt!” – Our top priority is to equip our students with both the certification and practical knowledge necessary to excel in their field. Through our optimized delivery format, which includes live instruction, hands-on labs, and rigorous exam preparation, we are able to produce unparalleled success rates. Our methodology has been proven to prepare students for real-world scenarios, ensuring that they are able to apply their skills with confidence.
Take your career to the next level with our instructor led, live online and onsite training!
EC-Council Computer Hacking Forensic Investigator Training. Exam Preparation and Training
Our training programs utilize concise, specially designed slides to facilitate a deeper understanding of complex security concepts. These slides are created by our expert developers and are aimed at providing an optimal learning experience. The course, led by Eric Reed – a Master Certified CompTIA Instructor and 9-time recipient of EC- Council’s Instructor of the Year award, spans a 5-day (or 10-evening) period and is designed to be highly interactive, featuring practical exercises to ensure that students acquire the necessary skills to succeed in the industry.