Price:
$1,795
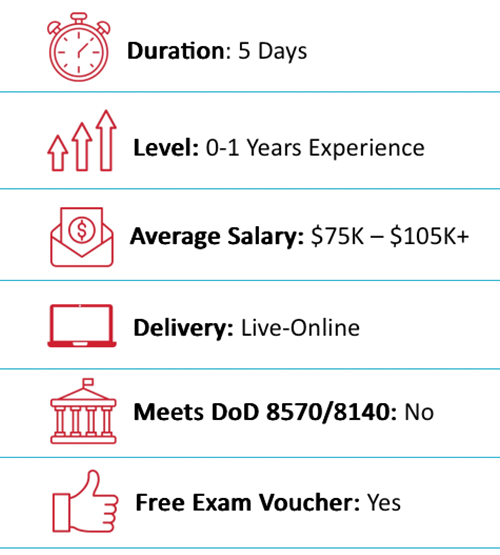
Duration:
5 Days or 10 Nights
Delivery Method:
Online Live/On-Demand Live
Overview
Outline
Training Includes
Audience
About Exam
About the Instructor
Eric Reed Exclusives

EC-Council E|CIH Overview
EC-Council’s Certified Incident Handler program equips students with the knowledge, skills, and abilities to effectively prepare for, deal with, and eradicate threats and threat actors in an incident.
This program provides the entire process of Incident Handling and Response and hands-on labs that teach the tactical procedures and techniques required to effectively Plan, Record, Triage, Notify and Contain. Students will learn the handling of various types of incidents, risk assessment methodologies, as well as laws and policies related to incident handling. After attending the course, students will be able to create IH&R policies and deal with different types of security incidents such as malware, email security, network security, web application security, cloud security, and insider threat-related incidents.

EC-Council E|CIH Outline
Module 1: Introduction to Incident Handling and Response
- Understand Information Security Threats and Attack Vectors
- Explain Various Attack and Defense Frameworks
- Understand Information Security Concepts
- Understand Information Security Incidents
- Understand the Incident Management Process
- Understand Incident Response Automation and Orchestration
- Describe Various Incident Handling and Response Best Practices
- Explain Various Standards Related to Incident Handling and Response
- Explain Various Cybersecurity Frameworks
- Understand Incident Handling Laws and Legal Compliance
Module 2: Incident Handling and Response Process
- Understand Incident Handling and Response Process
- Preparation for Incident Handling and Response
- Incident Recording and Assignment
- Incident Triage
- Notification
- Containment
- Evidence Gathering and Forensic Analysis
- Eradication
- Recovery
- Post-Incident Activities
- Information Sharing Activities
Module 3: First Response
- Explain the Concept of First Response
- Understand the Process of Securing and Documenting the Crime Scene
- Understand the Process of Collecting Evidence at the Crime Scene
- Explain the Process for Preserving, Packaging, and Transporting Evidence
Module 4: Handling and Responding to Malware Incidents
- Understand the Handling of Malware Incidents
- Explain Preparation for Handling Malware Incidents
- Understand Detection of Malware Incidents
- Explain Containment of Malware Incidents
- Describe How to Perform Malware Analysis
- Understand Eradication of Malware Incidents
- Explain Recovery after Malware Incidents
- Understand the Handling of Malware Incidents Case Study
- Describe Best Practices against Malware Incidents
Module 5: Handling and Responding to Email Security Incidents
- Understand Email Security Incidents
- Explain Preparation Steps for Handling Email Security Incidents
- Understand Detection and Containment of Email Security Incidents
- Understand Analysis of Email Security Incidents
- Explain Eradication of Email Security Incidents
- Understand the Process of Recovery after Email Security Incidents
- Understand the Handling of Email Security Incidents Case Study
- Explain Best Practices against Email Security Incidents
Module 6: Handling and Responding to Network Security Incidents
- Understand the Handling of Network Security Incidents
- Prepare to Handle Network Security Incidents
- Understand Detection and Validation of Network Security Incidents
- Understand the Handling of Unauthorized Access Incidents
- Understand the Handling of Inappropriate Usage Incidents
- Understand the Handling of Denial-of-Service Incidents
- Understand the Handling of Wireless Network Security Incidents
- Understand the Handling of Network Security Incidents Case Study
- Describe Best Practices against Network Security Incidents
Module 7: Handling and Responding to Web Application Security Incidents
- Understand the Handling of Web Application Incidents
- Explain Preparation for Handling Web Application Security Incidents
- Understand Detection and Containment of Web Application Security Incidents
- Explain Analysis of Web Application Security Incidents
- Understand Eradication of Web Application Security Incidents
- Explain Recovery after Web Application Security Incidents
- Understand the Handling of Web Application Security Incidents Case Study
- Describe Best Practices for Securing Web Applications
Module 8: Handling and Responding to Cloud Security Incidents
- Understand the Handling of Cloud Security Incidents
- Explain Various Steps Involved in Handling Cloud Security Incidents
- Understand How to Handle Azure Security Incidents
- Understand How to Handle AWS Security Incidents
- Understand How to Handle Google Cloud Security Incidents
- Understand the Handling of Cloud Security Incidents Case Study
- Explain Best Practices against Cloud Security Incidents
Module 9: Handling and Responding to Insider Threats
- Understand the Handling of Insider Threats
- Explain Preparation Steps for Handling Insider Threats
- Understand Detection and Containment of Insider Threats
- Explain Analysis of Insider Threats
- Understand Eradication of Insider Threats
- Understand the Process of Recovery after Insider Attacks
- Understand the Handling of Insider Threats Case Study
- Describe Best Practices against Insider Threats
Module 10: Handling and Responding to Endpoint Security Incidents
- Understand the Handling of Endpoint Security Incidents
- Explain the Handling of Mobile-Based Security Incidents
- Explain the Handling of IoT-Based Security Incidents
- Explain the Handling of OT-Based Security Incidents
- Understand the Handling of Endpoint Security Incidents Case Study

EC-Council E|CIH Training Includes
- 25-Year Veteran Instructor with Over 60,000 Students Trained and the Best Pass Rates in the Industry
- 10-Time EC-Council Instructor of the Year / 7-Time Instructor Circle of Excellence
- “Pass on the First Attempt!” Guarantee
- Online Live Instructor Led Training
- 1 Year Access to Training Session Recordings
- Official EC-Council Courseware
- Official Virtual Lab Environment
- Fast-Track Exam Preparation
- Written Exam Voucher
- Practical Exam Voucher
- After Class Support and Mentoring

EC-Council E|CIH Audience
- Security analysts
- SOC Analyst
- Incident responders
- Administrators
- Penetration testers
- Vulnerability auditors
- Cyber forensic investigator
- IT managers
- System and Network Administrator

About EC-Council E|CIH Exam
- Exam title: ECIH
- Exam code: 212-89
- Number of questions: 100
- Duration: 4 Hours
- Availability: ECC Exam, VUE
- Test Format: Multiple Choice

About the EC-Council E|CIH Instructor
Eric Reed is a nationally recognized cybersecurity instructor and founder of Eric Reed Cybersecurity Training, with over 25 years of experience developing mission-ready IT and security professionals. A Master Certified EC-Council Instructor and 10-time Instructor of the Year—including the 2024 CEH Instructor of the Year from EC-Council—Eric has trained more than 60,000 students worldwide across certifications including CompTIA Security+, CySA+, PenTest+, CISSP, and CEH.
Renowned for his engaging teaching style and unmatched pass rates, Eric has delivered training for leading organizations across defense, government, healthcare, finance, and technology—including Boeing, Lockheed Martin, Verizon, the U.S. Department of Defense, and the Mayo Clinic. His programs emphasize real-world application, DoD 8140/NICE alignment, and first-attempt success, helping individuals and teams strengthen their defenses and advance their careers in cybersecurity.
DoD 8570/8140-Approved:
Career Roles You Can Access with EC-Council E|CIH
 Not baseline listed
Not baseline listed
 Cyber Defense Incident Responder (531)
Cyber Defense Incident Responder (531)
 Cyber Defense Analyst (511)
Cyber Defense Analyst (511)
 Vulnerability Assessment Analyst (541)
Vulnerability Assessment Analyst (541)
 Forensics Analyst (531)
Forensics Analyst (531)
 Threat/Warning Analyst (671)
Threat/Warning Analyst (671)
What Job Titles are Most Common for People with EC-Council E|CIH Certification?
Some common positions that this certification can help you land include:
What our Students say
The Best ECIH Training In Orlando, FL With Eric Reed Cybersecurity Training
“Pass on the First Attempt!” – Our top priority is to equip our students with both the certification and practical knowledge necessary to excel in their field. Through our optimized delivery format, which includes live instruction, hands-on labs, and rigorous exam preparation, we are able to produce unparalleled success rates. Our methodology has been proven to prepare students for real-world scenarios, ensuring that they are able to apply their skills with confidence.
Take your career to the next level with our instructor led, live online and onsite training!
ECIH Training In Orlando, FL. Exam Preparation and Training
Our training programs utilize concise, specially designed slides to facilitate a deeper understanding of complex security concepts. These slides are created by our expert developers and are aimed at providing an optimal learning experience. The course, led by Eric Reed – a Master Certified CompTIA Instructor and 9-time recipient of EC- Council’s Instructor of the Year award, spans a 5-day (or 10-evening) period and is designed to be highly interactive, featuring practical exercises to ensure that students acquire the necessary skills to succeed in the industry.