
Price:
$3,495
Duration:
5 Days or 10 Nights
Delivery Method:
Online Live/On-Demand Live
Overview
Outline
Training Includes
Audience
About Exam
About the Instructor
Eric Reed Exclusives

Certified Ethical Hacker (CEHᵃᶦ) (v13) Overview
CEH v13 (CEHᵃᶦ) brings the world’s leading ethical-hacking certification into the age of AI. This evolved program expands coverage across 20 modules and more than 550 attack techniques, pairs knowledge content with a realistic cyber range, and adds AI-driven capabilities so you learn how attackers — and defenders — now use intelligent tools.
Our updated course experience gives you hands-on practice in realistic environments so you “live” through attacks and defensive responses. You’ll get access to hundreds of guided labs in a cloud-based cyber range and thousands of real-world tools so every course objective can be practiced on live targets.
What’s New & Why It Matters
-
AI-Enhanced Curriculum: Learn AI-augmented attack and defense techniques so you understand modern adversary workflows and how to harden systems against them.
-
Expanded Techniques & Modules: CEH v13 covers 20 modules and 550+ attack techniques, giving you broader, deeper threat coverage than prior versions.
- Cyber Range + CTFs: Practice in a cloud cyber range and gain year-long access to monthly CTF challenges to keep your skills sharp and earn continuing education credits.

Course Outline – CEHᵃᶦ (v13)
Module 1: Introduction to Ethical Hacking
- Information Security Overview
- Cyber Kill Chain Concepts
- Hacking Concepts
- Ethical Hacking Concepts
- Information Security Controls
- Information Security Laws and Standards
Module 2: Footprinting and Reconnaissance
- Footprinting Concepts
- Footprinting Through Search Engines
- Footprinting Through Web Services
- Footprinting Through Social Networking Sites
- Website Footprinting
- Email Footprinting
- Whois Footprinting
- DNS Footprinting
- Network Footprinting
- Footprinting Through Social Engineering
- Footprinting Tools
- Footprinting Countermeasures
Module 3: Scanning Networks
- Network Scanning Concepts
- Scanning Tools
- Host Discovery
- Port and Service Discovery
- OS Discovery Banner Grabbing and OS Fingerprinting
- Scanning Beyond IDS and Firewall
- Draw Network Diagrams
Module 4: Enumeration
- Enumeration Concepts
- NetBIOS Enumeration
- SNMP Enumeration
- LDAP Enumeration
- NTP and NFS Enumeration
- SMTP and DNS Enumeration
- Other Enumeration Techniques
- Enumeration Countermeasures
Module 5: Vulnerability Analysis
- Vulnerability Assessment Concepts
- Vulnerability Classification and Assessment Types
- Vulnerability Assessment Solutions and Tools
- Vulnerability Assessment Reports
Module 6: System Hacking
- System Hacking Concepts
- Gaining Access
- Escalating Privileges
- Maintaining Access
- Clearing Logs
Module 7: Malware Threats
- Malware Concepts
- APT Concepts
- Trojan Concepts
- Virus and Worm Concepts
- Fileless Malware Concepts
- Malware Analysis
- Countermeasures
- Anti-Malware Software
Module 8: Sniffing
- Sniffing Concepts
- Sniffing Technique MAC Attacks
- Sniffing Technique DHCP Attacks
- Sniffing Technique ARP Poisoning
- Sniffing Technique Spoofing Attacks
- Sniffing Technique DNS Poisoning
- Sniffing Tools
- Countermeasures
- Sniffing Detection Techniques
Module 9: Social Engineering
- Social Engineering Concepts
- Social Engineering Techniques
- Insider Threats
- Impersonation on Social Networking Sites
- Identity Theft
- Countermeasures
Module 10: Denial of Service
- DoS and DDoS Concepts
- DoS and DDoS Attack Techniques
- Botnets DDoS Case Study
- DoS and DDoS Attack Tools
- Countermeasures
- DoS and DDoS Protection Tools
Module 11: Session Hijacking
- Session Hijacking Concepts
- Application Level Session Hijacking
- Network Level Session Hijacking
- Session Hijacking Tools
- Countermeasures
Module 12: Evading IDS, Firewalls, and Honeypots
- IDS, IPS, Firewall, and Honeypot Concepts
- IDS, IPS, Firewall, and Honeypot Solutions
- Evading IDS
- Evading Firewalls
- IDS and Firewall Evading Tools
- Detecting Honeypots
- IDS and Firewall Evasion Countermeasures
Module 13: Hacking Web Servers
- Web Server Concepts
- Web Server Attacks
- Web Server Attack Methodology
- Web Server Attack Tools
- Countermeasures
- Patch Management
- Web Server Security Tools
Module 14: Hacking Web Applications
- Web Application Concepts
- Web Application Threats
- Web Application Hacking Methodology
- Web API, Webhooks, and Web Shell
- Web Application Security
Module 15: SQL Injection
- SQL Injection Concepts
- Types of SQL Injection
- SQL Injection Methodology
- SQL Injection Tools
- Evasion Techniques
- Countermeasures
Module 16: Hacking Wireless Networks
- Wireless Concepts
- Wireless Encryption
- Wireless Threats
- Wireless Hacking Methodology
- Wireless Hacking Tools
- Bluetooth Hacking
- Countermeasures
- Wireless Security Tools
Module 17: Hacking Mobile Platforms
- Mobile Platform Attack Vectors
- Hacking Android OS
- Hacking iOS
- Mobile Device Management
- Mobile Security Guidelines and Tools
Module 18: IoT and OT Hacking
- IoT Hacking
- IoT Concepts
- IoT Attacks
- IoT Hacking Methodology
- IoT Hacking Tools
- Countermeasures
- OT Hacking
- OT Concepts
- OT Attacks
- OT Hacking Methodology
- OT Hacking Tools
- Countermeasures
Module 19: Cloud Computing
- Cloud Computing Concepts
- Container Technology
- Serverless Computing
- Cloud Computing Threats
- Cloud Hacking
- Cloud Security
Module 20: Cryptography
- Cryptography Concepts
- Encryption Algorithms
- Cryptography Tools
- Public Key Infrastructure PKI
- Email Encryption
- Disk Encryption
- Cryptanalysis
- Countermeasures

Certified Ethical Hacker (CEHᵃᶦ) (v13) Training Includes
- 25-Year Veteran Instructor with Over 60,000 Students Trained and the Best Pass Rates in the Industry
- 10-Time EC-Council Instructor of the Year / 7-Time Instructor Circle of Excellence
- “Pass on the First Attempt!” Guarantee
- Online Live Instructor Led Training
- 1 Year Access to Training Session Recordings
- Official EC-Council Courseware
- Official Virtual Lab Environment
- Fast-Track Exam Preparation
- Written Exam Voucher
- Practical Exam Voucher
- After Class Support and Mentoring

Certified Ethical Hacker (CEHᵃᶦ) Audience
- Security officers
- Auditors
- Security engineers
- System administrators
- Penetration testers
- Network administrator
- IT managers

About Certified Ethical Hacker (CEHᵃᶦ) Exam
CEH v13 includes both a knowledge (multiple-choice) exam and a practical (hands-on) exam option to validate real-world skills:
-
Knowledge exam: 125 multiple-choice questions, standard testing duration and coverage across threat, detection, prevention, and methodology.
- Practical exam: A timed, scenario-based practical assessment (multi-hour) with real networked VMs and challenges to demonstrate applied ethical-hacking proficiency.
Completing the training prepares you to attempt the official CEH v13 exams and positions you for roles that require both theoretical knowledge and proven hands-on capability.

About the Certified Ethical Hacker (CEHᵃᶦ) (v13) Instructor
Eric Reed is a nationally recognized cybersecurity instructor and founder of Eric Reed Cybersecurity Training, with over 25 years of experience developing mission-ready IT and security professionals. A Master Certified EC-Council Instructor and 10-time Instructor of the Year—including the 2024 CEH Instructor of the Year from EC-Council—Eric has trained more than 60,000 students worldwide across certifications including CompTIA Security+, CySA+, PenTest+, CISSP, and CEH.
Renowned for his engaging teaching style and unmatched pass rates, Eric has delivered training for leading organizations across defense, government, healthcare, finance, and technology—including Boeing, Lockheed Martin, Verizon, the U.S. Department of Defense, and the Mayo Clinic. His programs emphasize real-world application, DoD 8140/NICE alignment, and first-attempt success, helping individuals and teams strengthen their defenses and advance their careers in cybersecurity.
Certified Ethical Hacker (CEH)
Upcoming Classes
Day Class
5 Days • 10 AM – 6 PM EST | $3,495
Night Class
10 Nights • 6:30 PM – 9:30 PM EST | $3,495
On-Demand
ELearning • Self paced online course | $3,495
Quick Facts
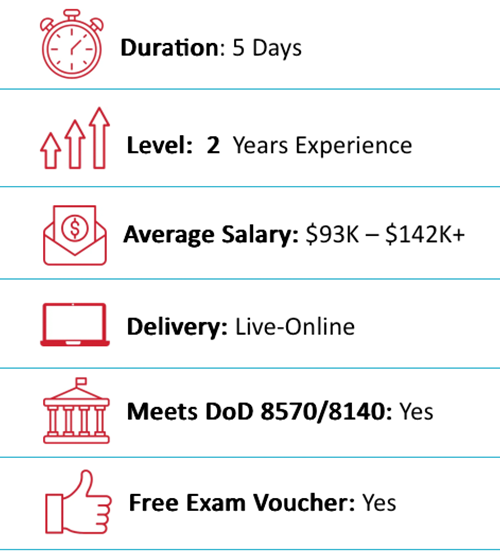
DoD 8570/8140-Approved:
Career Roles You Can Access with EC-Council CEH
 CSSP Analyst
CSSP Analyst
CSSP Infrastructure Support
CSSP Incident Responder
CSSP Auditor
 Penetration Tester (521)
Penetration Tester (521)
Cyber Defense Incident Responder (531)
Vulnerability Assessment Analyst (541)
Red Team Specialist (541)
Cyber Operator (521)
What Job Titles are Most Common for People with EC-Council CEH Certification?
Some common positions that this certification can help you land include:
What our Students say
The Best CEH Courses in Ashburn With Eric Reed Cybersecurity Training
“Pass on the First Attempt!” – Our top priority is to equip our students with both the certification and practical knowledge necessary to excel in their field. Through our optimized delivery format, which includes live instruction, hands-on labs, and rigorous exam preparation, we are able to produce unparalleled success rates. Our methodology has been proven to prepare students for real-world scenarios, ensuring that they are able to apply their skills with confidence.
Take your career to the next level with our instructor led, live online and onsite training!
CEH Courses in Ashburn. Exam Preparation and Training
Our training programs utilize concise, specially designed slides to facilitate a deeper understanding of complex security concepts. These slides are created by our expert developers and are aimed at providing an optimal learning experience. The course, led by Eric Reed – a Master Certified Instructor and 10-time recipient of EC- Council’s Instructor of the Year award, spans a 5-day (or 10-evening) period and is designed to be highly interactive, featuring practical exercises to ensure that students acquire the necessary skills to succeed in the industry.












